When building and managing an Azure environment, Microsoft maintains control of the network traffic as a core operations responsibility. The primary Azure platform resource to implement network traffic control is the Network Security Group (NSG). A Network Security Group allows you to define security rules, like firewall rules, that control traffic by specifying allowed and denied sources, destinations, ports, and protocols. Like all Azure resources, there are multiple options to manage NSGs, including the standard Azure Management tools: The Azure Portal, Scripts (PowerShell and CLI), APIs, and Azure Resource Manager (ARM) templates.
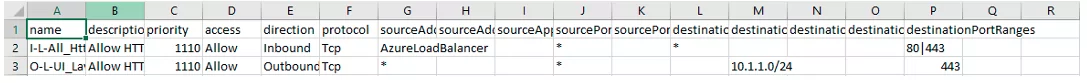
Managing NSG security rules using an ARM template can be challenging. Each security rule is defined using a large chunk of JSON, and many security rules may be required. The verbose JSON structure makes it difficult to see many rules at once, visualize changes from version to version, and encourage team members to revert to the Azure Portal to view and edit rules. Why use the Azure Portal? It turns out the portal’s grid format for NSG Security Rules was comfortable for quickly viewing multiple rules and for making minor edits to individual rules.
Since the portal’s grid view was comfortable the CSV file format seemed like the right idea based on its similarity to a grid. CSV files have a few pros:
- Good viewers and editors including Excel and VS Code.
- One vertically compact line for each security rule.
- A vertically compact view that makes it easier to visually scan rules and to see the changes that are made from version to version when viewing differences.
- Anyone who can edit a CSV can edit the NSG Security Rules allowing a larger group of security rule editors.
NSG in JSON format
This is a simple example of the NSG Security Rule JSON. A rule like this can get much larger vertically when numerous ports and address prefixes are defined:
{
"name": "I-L-All_HttpHttps-UI_Layer-T",
"description": "Allow HTTP + HTTPS traffic inbound.",
"priority": 1110,
"access": "Allow",
"direction": "Inbound",
"protocol": "Tcp",
"sourceAddressPrefix": "",
"sourceAddressPrefixes": [
"AzureLoadBalancer"
],
"sourceApplicationSecurityGroups": null,
"sourcePortRange": "*",
"sourcePortRanges": null,
"destinationAddressPrefix": "*",
"destinationAddressPrefixes": null,
"destinationApplicationSecurityGroups": null,
"destinationPortRange": "",
"destinationPortRanges": [
"80",
"443"
]
}
NSG in CSV Format
Excel
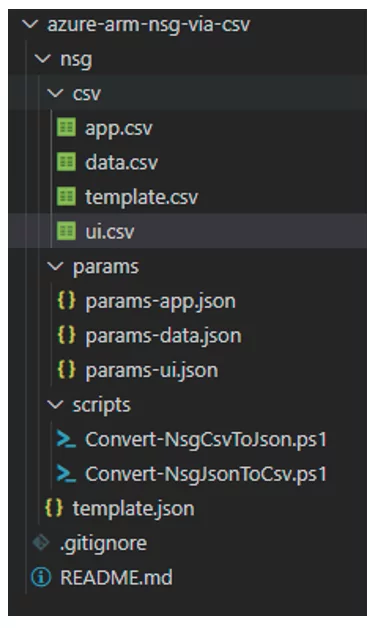
Converting Between CSV and JSON
The transition from CSV to JSON and from JSON back to CSV must be repeatable and simple. In this scenario, PowerShell scripts manage this process: Convert-NsgCsvToJson.ps1 and Convert-NsgJsonToCsv.ps1.
The Convert-NsgCsvToJson.ps1 script is straightforward and does the following:
- Read the source CSV file.
- Read the destination JSON file.
- Split multi-value fields into an array based on the parameter: CsvArraySeparator. The default is the pipe character ‘|’. For fields like source and destination port ranges, this collapses multiple values into a single CSV field.
- Structure of the CSV format data into objects that match the ARM Template NSG Security Rule JSON structure.
- Use a JsonFileType parameter to determine where in the destination JSON structure to place the security rules array. This allows placement of the security rules array into a parameter file, template file, or into an empty JSON file.
A New Workflow
With PowerShell scripts, the new workflow for NSGs is:
- Create and edit NSG Security Rules in a CSV file – usually using Excel.
- Visually scan the CSV looking for obvious anomalies (Excel makes it easy to see when one rule stands out from the others and as an example, a value is in the wrong column).
- Execute the script: Convert-NsgCsvToJson.ps1 to convert the rules to the Json Structure and update the destination JSON file.
- Deploy the ARM Template and updated parameters file to a dev/test environment using standard deployment approaches such as the Azure CLI. This will fully validate the NSG Json prior to production deployment.
- Deploy to Production during a planned change window.
From JSONback to CSV
At times, a team member may change the portal, for example, during troubleshooting. Once an update is made in the portal, transfer Azure changes back to the code that defines this infrastructure. The CSV files are the canonical source, so there needs to be a process to return to CSV from JSON.
- To retrieve the NSG Security Rules from the portal execute a CLI command to retrieve NSG security rules and export them to a JSON File.
az network nsg rule list --nsg-name subnet-01-nsg --resource-group net-rgp-01 | set-content subnet-01-export.json
- Execute the Convert-NsgJsonToCsv.ps1 script using the generated file as the input and the corresponding CSV file as the output.
Constraints
The environment these scripts were built for may not match your own. This environment includes several constraints:
- Azure Resource Manager Templates are the language for Azure Infrastructure as Code.
- Manual steps are required: automated build and release pipelines are not yet available.
- There is no guarantee that NSG security rules will not be modified in the Azure Portal, so a mechanism is required to synchronize the code with the environment.
Future Improvements
This solution represented a significant improvement for this team instead of managing NSG security rules directly in the JSON format. As with every answer, there are ideas on how to improve. Here are a few that have come to mind:
- Use CI/CD tools such as GitHub Actions to automatically execute the Convert-NsgJsonToCsv.ps1 script when an NSG CSV file is committed.
- Implement a release pipeline so that modified NSG Csv files trigger the conversion script, wait for approval to deploy, and deploy the ARM Template to the dev/test environment.
- Add Pester tests to the PowerShell scripts.
- Try this approach with other IaC languages such as Terraform.
Additional Notes
- The example template has been dramatically simplified.
- The production template also configures NSG Diagnostic Settings and NSG Flow Logs.
- The production template builds all resource names based on several segments defined in a naming convention.
- There are NSG Security Rules that are considered baseline rules that should be applied to every NSG. These rules are managed in a CSV file and placed in an array in the base template and not repeated in each parameter file. An example of this is a rule that allows all servers to contact the organization’s DNS servers.
- Application Security Groups are used to group servers in the local VNET so that NSG Security Rules do not need to include IP addresses for servers contained in the VNET. The only IP Address Prefixes specified directly in our rules are from outside the current VNET. As with the NSGs, this template defines ASGs in the template (baseline) and parameters file (local) combined and created during template deployment. Only the unique portion of the name is used to define the group, and to specify rules. The remainder of the term is built during deployment. ASGs in Azure are currently only valid for the VNET where they are created, and only one ASG may be specified per security rule. This script creates all the ASGs defined in the template and parameters file.
Code
The code for these scripts including the conversion scripts and a sample ARM Template, ARM Template Parameters files, and matching NSG Security Rule CSV files is available on GitHub: https://github.com/matthew-dupre/azure-arm-nsg-via-csv