Welcome to part five of our blog series based on my latest PluralSight course: Applied Azure. Previously, we’ve discussed Azure Web Sites, Azure Worker Roles, Identity and Access with Azure Active Directory and Azure Service Bus and MongoDB.
Welcome to part five of our blog series based on my latest PluralSight course: Applied Azure. Previously, we’ve discussed Azure Web Sites, Azure Worker Roles, Identity and Access with Azure Active Directory and Azure Service Bus and MongoDB.
Motivation
Let’s face it, security, privacy and compliance are the key concerns when it comes to adopting any public cloud platform. To alleviate such concerns, Windows Azure team has setup a Windows Azure Trust Center website to provide the latest updates on these topics. Windows Azure complies with several international, country and industry-specific compliance requirements including ISO 27001, FedRAMP, PCI-DSS and HIPAA. In this blog post we are going to focus on building HIPAA compliant applications on the Windows Azure platform.
HIPAA (Health Insurance Portability and Accountability Act) is a US Law that applies to doctor’s offices, hospitals, insurance companies and other companies (including IT companies) that have access to patient information (called PHI – Protected Health Information). The law requires that anyone, directly or indirectly, handling PHI sign a written agreement (known as BAA – Business Associate Agreement) to adhere to certain security and privacy provisions set forth in the HIPAA law.
The Technical safeguards section of HIPAA specifies standards in the following areas for protection of PHI.
- Access control – Only allow access to persons and software that have been granted access.
- Audit controls – Record and examine all activity to access PHI data.
- Integrity – Data is not improperly altered or destroyed without detection.
- Person or entity authentication – Assign a unique name and/or number for identifying and tracking user identity.
- Transmission security – Ensure that the data is securely transmitted.
Windows Azure offers several building blocks that are HIPAA compliant. This means that Microsoft is willing to offer a BAA to its Windows Azure customers can be a big deal if you are building applications that require HIPAA compliance.
Scenarios
Let us assume that you are tasked with building a HIPAA compliant web application. In the past, such applications have been built from the ground-up and hosted on-premises in order to retain total control over all aspects of security and compliance. In this environment you would have to be responsible for signing the BAA for all aspects of the application, including the application logic, data, building blocks, databases and of course the infrastructure used to host the application (including physical safeguards such as facility access). Building such an application on Windows Azure potentially offers you a way to leverage the BAA Microsoft is offering. This means you don’t have to be responsible for all of things we listed earlier. Of course you are still responsible for the application functionality (e.g. preventing a cross site scripting attack on the web pages you develop is still your responsibility).
Core Concept
As of now, Windows Azure offers the following building blocks that are HIPAA compliant:
- Cloud Services (Web and Worker roles)
- Storage (Tables, Blobs, Queues)
- Virtual Machines (Infrastructure-as-a-Service)
- Networking (Windows Azure Connect, Traffic Manager, and Virtual Network)
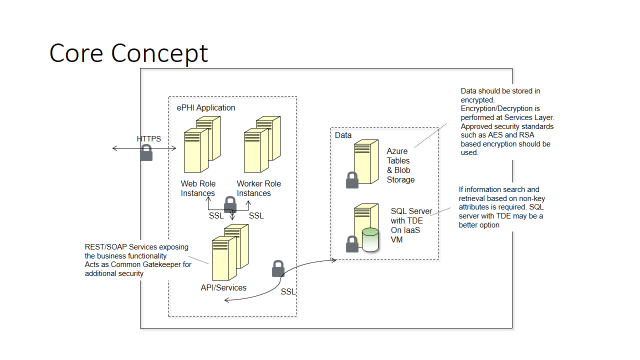
The following diagram depicts the high level architecture of a web application that is designed to meet the HIPAA compliance requirement. It involves leveraging the aforementioned Windows Azure Building blocks in order to comply with the requirements listed in technical safeguards. It uses Web and Worker Roles to host the application logic. All data transmission is over SSL and Windows Azure storage is used as the persistence store. All data stored in Windows Azure storage is encrypted using a custom encryption library and Windows Azure storage analytics logs are enabled to capture successful and failed requests to access data.
Design Considerations
Here are some design considerations when building HIPAA compliant applications on the Windows Azure platform:
- HIPAA compliance is a shared responsibility between you and Microsoft. Microsoft offers BAA for certain Windows Azure platform building blocks. Securing application logic and data is still your responsibility.
- Even though Windows Azure storage is HIPAA compliant you will need to encrypt the data stored in it to comply with the HIPAA technical safeguards.
- Services such as Windows Azure SQL Database because of their multi-tenant design are not part of the HIPAA compliance.
- Recently added features such Windows Azure operational logs that provide a historical log of all operations performed against compute instances are important for detecting unauthorized alteration or deletion of resources.
Summary
Windows Azure platform offers various building blocks that are HIPAA compliant. Microsoft also offers a HIPAA BAA to help meet the compliance requirements. However, it is important to know which features are currently in scope for the HIPAA BAA. Designing your applications using the features that are in scope is obviously key. While we focused on HIPAA in this blog post, you can use a similar approach to build applications that comply with other compliance standards.
Finally it is important to note that even though Windows Azure includes features to help with HIPAA compliance, you are responsible for ensuring that the way you use Windows Azure complies with HIPAA.
Disclaimer: This blog post is not intended to constitute legal advice. You are advised to seek the advice of legal counsel regarding compliance with HIPAA for your application development.