The Current Situation
Today, organizations continue the transition to cloud computing as part of their digital transformation journey and become highly productive organizations in their respective industry. While transitioning to cloud computing demonstrates agility, scalability, cost-effectiveness, and performance, the challenge is strengthening their security foundation and reducing risk. While vendors, such as Microsoft, provide the best-in-class measures and features for tightening the organization’s security foundation, the ultimate responsibility belongs to the specific organization. Of course, organizations will take precautionary steps for protecting device assets and data from malicious exfiltration and theft. Still, organizations tend to loosely protect the number one crucial asset: the user’s identity. As reported by Microsoft, cybersecurity experts detected and reported 15 million attacks, scoped to password-based attacks alone. This is a signal that the user’s password is the primary target! So, the big question is…how does an organization protect the user identity, device assets, and corporate data, preventing compromises and breaches? The answer: Zero Trust.
What is Zero Trust?
Top cybersecurity experts and leaders changed the game with the introduction and indoctrination of Zero Trust, revealed as the top method to protecting identities, assets, data, and the overall organization. First, let’s start with the basics: what is Zero Trust?
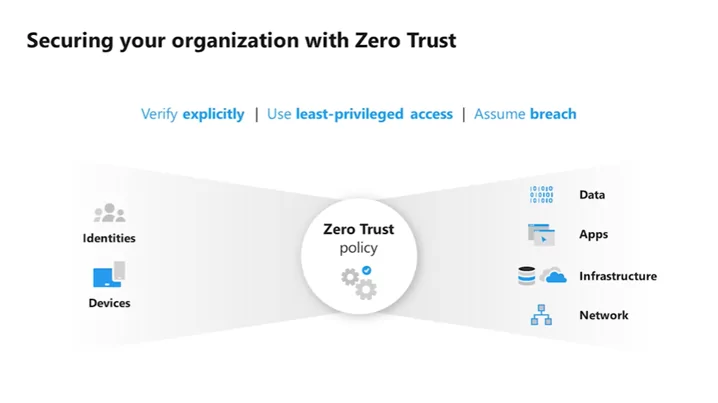
Microsoft clearly defines Zero Trust by following three objectives:
- Verify explicitly
- Use least-privileged access
- Assume breach
To summarize, treat every request as if it came from an unknown network and always verify.
Verify explicitly – the user identity is the key to accessing organizational data and assets. Therefore, the first step is to verify the identity belongs to the user accessing the data—Azure AD supplements this concept with Conditional Access and leveraging security features, such as multi-factor authentication.
Ask yourself these questions:
- Is the user accessing the data from the correct device to take it a step forward?
- Is it in the correct location?
- Is the user now at high risk?
- Is the device at high exposure due to an existing cybersecurity incident? Is the device compliant?
Use least-privileged access – not a new concept, but not a heavily practiced concept. Specifically, in Microsoft 365, organizations utilize privileged identities for administrative functions and operations. However, remember that organizations do not separate privileged access from their regular accounts and leave a permanent assignment for privileged access even if the identities are separate. Also, some organizations allow users to consent for apps accessing Microsoft 365 data. Azure AD offers features to reduce the risk revolving around privileged access and tracking identities. For example, Azure AD Privileged Identity Management, Microsoft Defender for Identity, Conditional Access, Azure AD Identity Governance, Azure AD Identity Protection, Microsoft Information Protection, and more.
Assume breach – As any cybersecurity expert, vendor, or leader will tell you, an organization will never reach 100% hardened as malicious actors and attackers continue to develop sophisticated attacks. Therefore, the organization must adopt the “assume breach” mindset and always defend themselves. Thus, Microsoft Defender for Office 365, Microsoft Defender for Endpoint, Microsoft Defender for Identity, and Microsoft Cloud App Security protect the organization from modern attacks, allowing an organization to become proactive and leverage advanced hunting features to prevent future malicious attacks. Other methods of adopting the “assume breach” mindset are reviewing user sign-in risk, device health risk and exposure, threat and vulnerability management, device & user identity hygiene, and more.
Why Microsoft Security for Zero Trust Foundation?
In brief, Microsoft defines security under four (4) pillars: protect everything, simplify the complex, catch what others miss, and grow your future.
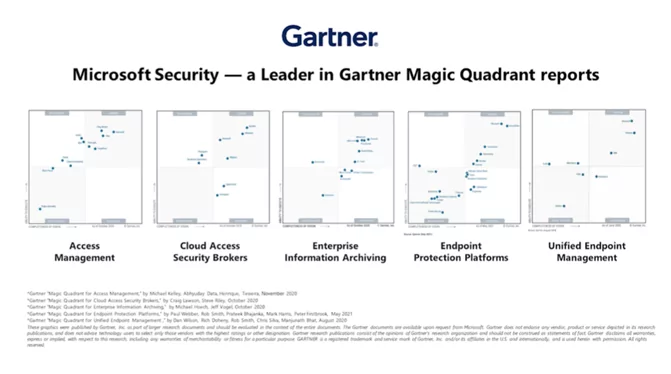
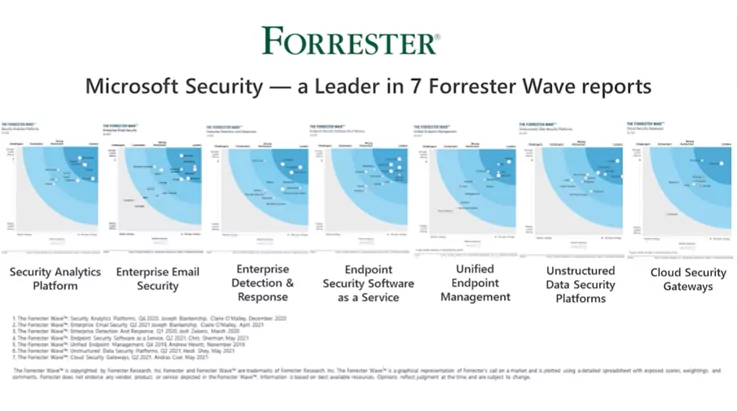
The four (4) pillars outline the overall position on Microsoft Security and the value it demonstrates for all customers: simplifying the Zero Trust foundation. In addition, Microsoft Security is proving its firm establishment in the cybersecurity field by being a prime leader in seven (7) Forrester Wave reports, and five (5) Gartner Magic Quadrant reports.
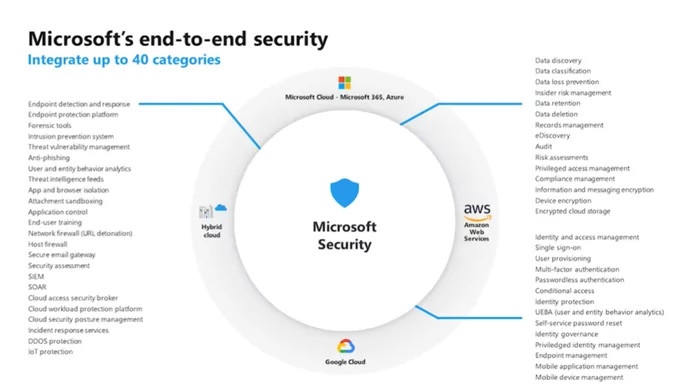
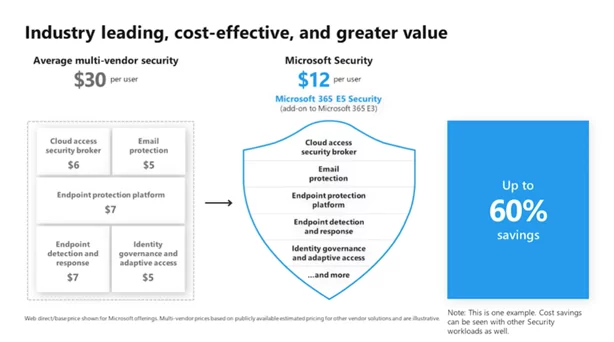
Microsoft Security continues to develop an end-to-end approach, integrating with a total of 53 essential categories around the cybersecurity landscape. It also demonstrates cost savings with Microsoft security solutions covered under Microsoft 365 E3 and Microsoft 365 E5 licensing tiers, compared to competitors in cybersecurity, such as Symantec, Cisco, and CrowdStrike.
How Can AIS help?
As a Microsoft Gold Partner, AIS contains the expertise and skills to assess, guide, and deploy the Zero Trust foundation from leveraging the solutions from the Microsoft Security foundation, such as Microsoft Defender for Endpoint, Microsoft Defender for Office 365, Microsoft Defender for Identity, Microsoft Cloud App Security, Microsoft Information Protection, Azure AD Privileged Identity Management, and more. Below is the Zero Trust Guidance Center from Microsoft. Consider AIS for assistance on this journey for your organization to be at an optimal state of the Zero Trust foundation!
Zero Trust Guidance Center: Zero Trust Guidance Center | Microsoft Docs